All articles containing the tag [
Geoip
]-
Troubleshooting Location Problems: How To Diagnose Connection Failures Based On Malaysian Server Address
connection fault location and troubleshooting guide for malaysian server addresses, covering practical diagnostic steps and suggestions such as ip/asn collection, ping/traceroute, dns resolution, tcp connectivity, routing and bandwidth.
malaysia server address connection failure troubleshooting diagnosis ping traceroute dns routing packet loss -
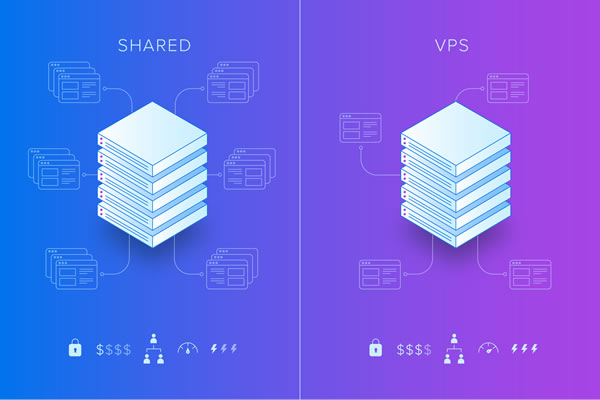
Detailed Explanation Of Malaysia Server Settings And Firewall Strategies In Vps Environment From Scratch
detailed explanation of malaysian server settings and firewall strategies in vps environment from scratch, including node selection, system configuration, network and storage optimization, ssh and protection, iptables/nftables practice, application layer protection and monitoring suggestions to help improve availability and security.
malaysia vps vps settings malaysia servers firewall policies ssh security iptables nftables waf network optimization data sovereignty -
How To Quickly Find Where The Korean Native Cloud Server Is And Complete Secure Access And Monitoring Configuration
this article introduces how to quickly locate the location of korean native cloud servers, and provides practical steps for secure access and monitoring configuration to help operation and security personnel improve visibility and stability.
korean native cloud server korean cloud server positioning secure access monitoring configuration geoip traceroute cloud console -
Security Recommendations: How To Protect Websites Built With Korean Native Ips From Ddos And Abnormal Access Risks
security suggestions for building websites using native ip in south korea, covering practical strategies such as ddos protection, abnormal access identification, border defense, monitoring and alarming, elastic expansion and compliance, to help reduce operational risks and improve availability.
korean native ip ddos protection abnormal access website security korean server waf cdn security suggestions -
How To Match Japanese Native Ip In Common Scenarios And How To Configure It If You Want High Availability
this article introduces japanese native ip matching methods and high-availability configuration ideas in common scenarios, including scenario division, ip planning, bgp/anycast, multi-outlet redundancy, load balancing and monitoring suggestions, to help build a stable japanese node architecture.
japanese native ip japanese ip high availability bgp redundancy anycast load balancing geoip ip planning multi-line export -
Query Tutorial Hong Kong Native Ip Segment Online Tool And Command Line Quick Verification Steps
this query tutorial outlines how to use online tools and command lines to quickly verify hong kong's native ip range. it includes step instructions, common command examples and precautions, and is suitable for network operation and maintenance and security verification.
hong kong native ip segment query tutorial online tools command line ip verification geoip asn whois -
Deployment And Maintenance Points For Using American Static Vps To Ensure Stable Access To Foreign Trade Platforms
this article introduces the deployment and maintenance key points of using american static vps to ensure stable access to foreign trade platforms, covering network planning, security configuration, load balancing, monitoring and operation and maintenance practices, aiming to improve the availability and compliance of foreign trade sites.
american static vps static vps stable access to foreign trade platform vps deployment overseas servers website availability -
Network Security Reinforcement And Compliance Recommendations For Deploying Servers In Cambodia (CN2) That Connect Back To Domestic Networks In China
Cybersecurity reinforcement and compliance recommendations for deploying servers in Cambodia that connect back to China, covering practical strategies such as compliance assessments, link and routing optimization, firewalls, DDoS protection, host hardening, log auditing, and cross-border data compliance.
Cambodia CN2: Home Country Server Network Security Compliance DDoS Protection Data Encryption Log Auditing Cross-border Transmission and Localization Compliance -
Network Security Reinforcement And Compliance Recommendations For Deploying Servers In Cambodia (CN2) That Connect Back To Domestic Networks In China
Cybersecurity reinforcement and compliance recommendations for deploying servers in Cambodia that connect back to China, covering practical strategies such as compliance assessments, link and routing optimization, firewalls, DDoS protection, host hardening, log auditing, and cross-border data compliance.
Cambodia CN2: Home Country Server Network Security Compliance DDoS Protection Data Encryption Log Auditing Cross-border Transmission and Localization Compliance